In the ever-expanding digital universe, a fundamental tension defines our modern lives: the trade-off between seamless convenience and personal privacy. At the heart of this debate stands Apple, a titan of technology that has staked its brand identity on safeguarding user data. Through sophisticated on-device and cloud-based encryption, the company has built a digital fortress around its users. However, this fortress is now under siege. Governments and law enforcement agencies worldwide are increasingly demanding a key to its gates, arguing that unbreakable encryption creates a lawless sanctuary for criminals. This escalating conflict, a recurring theme in Apple privacy news, is more than just a corporate dispute; it’s a battle that will define the future of digital privacy, security, and civil liberties for a generation. This article delves into the technical underpinnings of Apple’s security, the arguments fueling this global impasse, and the profound implications for every user within the vast Apple ecosystem news landscape.
The Digital Fortress: A Deep Dive into Apple’s Encryption Ecosystem
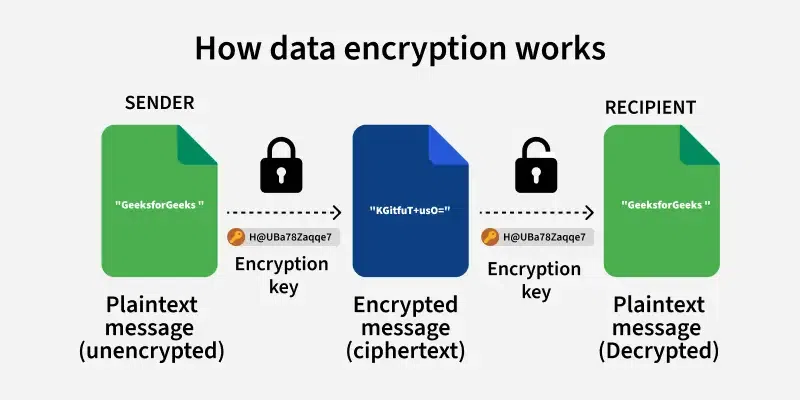
To understand the current conflict, one must first appreciate the intricate layers of security Apple has engineered across its products. This isn’t a simple password lock; it’s a multi-faceted architecture designed to make user data inaccessible to everyone but the user themselves—including Apple. This philosophy is a cornerstone of recent iOS security news and is built on several key pillars.
The Foundation: On-Device Encryption and the Secure Enclave
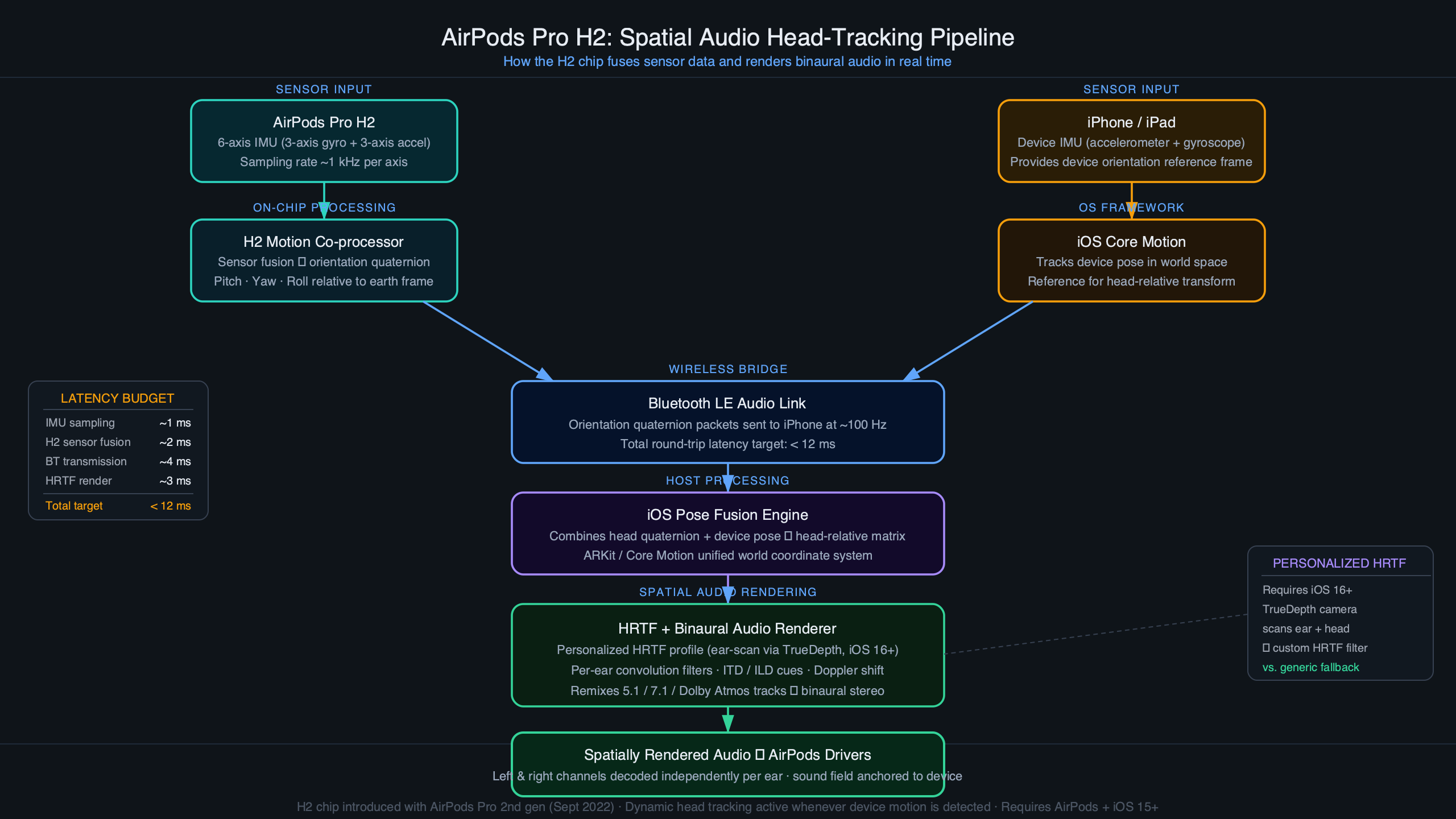
The first line of defense is the device itself. Every iPhone, iPad, and Mac contains a dedicated security coprocessor called the Secure Enclave. This hardware component is physically isolated from the main processor and runs its own microkernel, creating a secure vault for your most sensitive information. When you set a passcode or configure Face ID/Touch ID, the cryptographic keys used to encrypt and decrypt the data on your device’s storage are protected within this enclave. This means that everything from your iMessages and photos to your sensitive health data is encrypted at rest. Without your passcode or biometric authentication, the data is nothing more than unintelligible gibberish. This robust on-device security is why major iOS updates news frequently includes enhancements to the Secure Enclave’s functionality, ensuring that even the data streams from an Apple Pencil or paired AirPods Pro are protected by the host device’s core security.
The Cloud Conundrum: Standard vs. Advanced Data Protection for iCloud
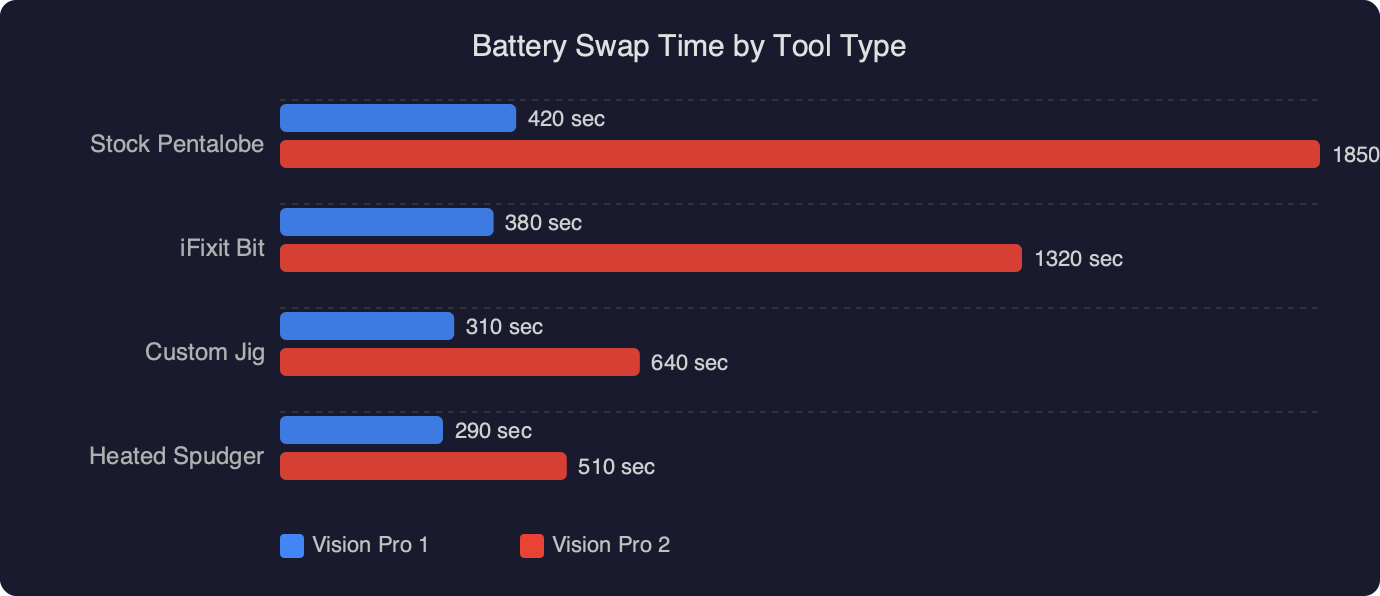
While on-device encryption is formidable, the real battleground is in the cloud. For years, Apple’s standard iCloud protection offered a hybrid model. Your data was encrypted in transit and stored encrypted on Apple’s servers. However, for key services like iCloud Backup, Photos, Notes, and Messages in iCloud, Apple retained a copy of the encryption keys. This was a practical decision, allowing Apple to help users recover their data if they forgot their password. But it also created a potential point of access for law enforcement with a valid warrant—Apple could, in theory, use its key to decrypt a user’s iCloud backup and provide it to authorities.
Recognizing this vulnerability, Apple recently introduced a major security upgrade: Advanced Data Protection for iCloud. When a user opts into this feature, it extends end-to-end encryption (E2EE) to the vast majority of iCloud services, including backups. With E2EE, the encryption keys are generated and stored exclusively on the user’s trusted devices (their iPhone, iPad, Mac). Apple no longer holds the keys and therefore has no technical ability to decrypt the user’s data. This move was a landmark piece of Apple privacy news, effectively locking the door and throwing away the key, placing control squarely in the hands of the user.

A Clash of Ideals: Law Enforcement Needs vs. User Privacy Absolutes
Apple’s move toward ubiquitous end-to-end encryption has put it on a direct collision course with governments who see it as a significant impediment to public safety. This clash is not new, but the stakes are higher than ever.
The Government’s Argument: The “Going Dark” Problem
Law enforcement agencies argue that the proliferation of unbreakable encryption is causing them to “go dark.” They contend that criminal investigations, from terrorism to child exploitation, increasingly hit a digital brick wall. A suspect’s iPhone or iCloud account might contain critical evidence—plans, contacts, locations—but if it’s protected by E2EE, that evidence is permanently inaccessible. From this perspective, tech companies are creating digital safe havens that are beyond the reach of the law. This has led to demands for “exceptional access” or “technical backdoors”—a special mechanism that would allow the government, with a legal warrant, to bypass encryption. They argue that such access is vital for national security and for bringing criminals to justice.
Apple’s Counterargument: The Pandora’s Box of Backdoors
Apple, along with a chorus of cryptographers and civil liberties advocates, vehemently opposes this demand. Their position, famously articulated during the 2016 San Bernardino iPhone case, is that a backdoor for the “good guys” is inevitably a backdoor for everyone else. The technical argument is straightforward: you cannot build a secure system with a deliberate flaw. Any special access key or vulnerability created for law enforcement could be discovered and exploited by malicious hackers, foreign adversaries, or repressive regimes. It would weaken the security of every user, from journalists and activists to everyday citizens. Creating such a tool would set a dangerous precedent, inviting requests from governments worldwide and fundamentally undermining the trust users place in their devices. This debate touches every product, from the data synced by an Apple Watch to the viewing habits on an Apple TV.
The Ripple Effect: What This Means for You and the Future of Technology
This high-stakes debate is not an abstract technical or legal argument. Its outcome will have tangible consequences for users, the technology industry, and the very fabric of our digital society.
For the Everyday User: Your Data, Your Choice

The core of this issue is about control. The outcome determines who is the ultimate arbiter of your personal data. Is it you, or is it a third party? For users, the most immediate and actionable insight is the power they now have with Advanced Data Protection. Enabling this feature is a conscious choice to prioritize privacy over the convenience of data recovery assistance from Apple. This is particularly critical when considering the sensitivity of modern data. The latest Apple health news highlights how devices now track incredibly personal medical information. Similarly, the rise of devices like the HomePod mini and the data collected by Siri news updates mean our homes are filled with sensors. Even an innocuous device like an AirTag has been at the center of privacy discussions. Protecting this vast trove of personal information begins with understanding and utilizing the tools available.
For the Tech Industry: A Precedent-Setting Battle
While Apple is currently in the spotlight, this is an industry-wide challenge. A legal or legislative precedent forcing Apple to weaken its encryption would inevitably be applied to Google, Meta, Signal, and every other company that provides secure communication or cloud storage. It could usher in an era where technology companies are mandated to build less secure products, fundamentally changing their role from data protectors to potential arms of state surveillance. The entire landscape of iPhone news and tech development would shift from building more secure systems to building compliant ones.
The Future of Privacy: AR, AI, and Beyond
Looking ahead, the stakes become exponentially higher. The latest Apple Vision Pro news heralds the dawn of spatial computing. This new class of devices will collect unprecedented types of data: what we look at via eye-tracking, the layout of our private homes, and our biometric responses to stimuli. The latest Apple AR news suggests a future where our digital and physical worlds are seamlessly blended. The question of who can access this deeply intimate data is paramount. Whether discussing a future iPod revival or a new accessory like a hypothetical Vision Pro wand, the underlying principles of data encryption being debated today will form the foundation of safety for tomorrow’s technology. Protecting this future is a key motivation behind Apple’s uncompromising stance.
Practical Steps for a More Secure Digital Life
While the larger battle unfolds in courtrooms and parliaments, users can take concrete steps to fortify their own digital privacy within the Apple ecosystem. This is not about being paranoid; it’s about being proactive in a world where our personal data is our most valuable asset.
Best Practices for Apple Users
-
Enable Advanced Data Protection: This is the single most important action you can take. Navigate to Settings > [Your Name] > iCloud > Advanced Data Protection and turn it on. Be sure to set up a recovery contact or recovery key, as Apple will not be able to help you regain access if you’re locked out.
-
Use a Strong Alphanumeric Passcode: A simple 6-digit PIN is good, but a longer, more complex passcode provides significantly stronger protection for the encryption keys stored in the Secure Enclave.
-
Review App Permissions Regularly: The latest iOS updates always bring new privacy controls. Regularly check which apps have access to your location, contacts, microphone, and photos. Limit access to only what is necessary.
-
Secure Your Apple ID: Your Apple ID is the key to your digital kingdom. Ensure Two-Factor Authentication is enabled. It provides a critical second layer of security that prevents unauthorized access even if someone steals your password.
This debate has evolved dramatically from the days of the iPod Classic or iPod Shuffle, when the most personal data on a device was a music library. Today, our devices hold the keys to our entire lives, from our finances and health records to our private conversations and memories. Protecting them is a shared responsibility.
Conclusion: The Unwritten Future of Digital Privacy
The ongoing tension between Apple and global governments over encryption is far more than just the latest headline in tech. It represents a fundamental crossroads for our digital society. On one path lies a future where user data is protected by default, empowering individuals with digital sovereignty and security. On the other path, privacy is conditional, subject to a “key under the doormat” that could be used by anyone who finds it. Apple’s staunch defense of end-to-end encryption is a high-stakes gamble on the principle that the best way to protect everyone is to build systems that are secure against everyone, without exception. The resolution of this impasse will not be simple, but its outcome will echo for decades, shaping the trust we place in the technology that is woven into the very fabric of our lives and setting the privacy standards for the next generation of innovation.