The New Frontier of iOS Security: Analyzing the Risks and Rewards of Alternative App Stores
For years, the Apple ecosystem has been synonymous with robust security and user privacy, a reputation built on the foundations of its tightly controlled “walled garden.” This approach, centered around the singular, heavily vetted App Store, has been a cornerstone of the user experience, offering a level of trust and safety that is a key differentiator in the mobile landscape. However, recent regulatory shifts are fundamentally altering this landscape, ushering in an era of alternative app marketplaces on iOS. This development represents one of the most significant changes in the history of the platform, raising critical questions for users, developers, and security professionals alike. As we navigate this new frontier, it’s essential to conduct a comprehensive technical analysis of what this means for the security model that millions have come to rely on. This article delves into the core principles of Apple’s traditional security architecture, contrasts it with the models proposed by new marketplaces, and provides actionable insights for users to safely manage their digital lives in this evolving environment, a topic at the forefront of recent iOS security news.
The Foundation of iOS Security: Deconstructing Apple’s Walled Garden
To understand the implications of alternative app stores, one must first appreciate the multi-layered security framework Apple has meticulously built. This framework is not a single feature but a synthesis of hardware, software, and policy designed to protect users from malware, fraud, and privacy intrusions. The latest Apple ecosystem news often highlights these features, but understanding how they work together is key.
The App Store Review Process: The First Line of Defense
At the heart of Apple’s security model is the mandatory App Store Review. Before any application is made available to the public, it undergoes a rigorous inspection by both automated systems and human reviewers. This process is far more than a simple malware scan. Apple’s guidelines scrutinize apps for a wide range of potential issues:
- Malicious Code: Apps are checked for known malware, spyware, and code that could compromise the device or user data.
- Privacy Violations: Reviewers verify that an app’s data collection practices align with its stated purpose and Apple’s stringent privacy policies. They check for clandestine tracking, misuse of APIs, and ensure that requests for sensitive data are justified and transparent. This is a crucial aspect of Apple privacy news.
- Functionality and Fraud: The review process weeds out fraudulent apps, such as those that mimic legitimate services to steal credentials or those that use deceptive billing practices.
- Content and Safety: Apps are also reviewed for inappropriate content, ensuring a safe environment, especially for younger users.
This comprehensive gatekeeping ensures that from the latest iPhone news apps to complex creative tools for iPad, the software users download has met a high baseline for safety and quality.
Sandboxing and System-Level Protections
Beyond the review process, iOS itself is architected for security. The most critical principle is “sandboxing.” Every app on iOS runs in its own restricted environment, or sandbox. It has access only to its own data and cannot access system files or the data of other applications without explicit permission granted by the user through a system prompt. This containment strategy means that even if a malicious app were to somehow make it onto a device, its ability to cause widespread damage is severely limited. This fundamental protection extends to all devices, from an iPhone to an Apple TV, and is a frequent topic in Apple TV marketing news when discussing user safety.
This is further fortified by other technologies:
- Code Signing: All apps must be cryptographically signed by Apple. This guarantees that the app was approved by Apple and has not been tampered with since it was signed.
- Secure Enclave: A dedicated hardware-based security processor that handles sensitive data like Face ID, Touch ID, and Apple Pay credentials, keeping it isolated from the main processor and iOS itself.
- Permissions System: Apps must explicitly ask the user for permission to access sensitive information or hardware, such as location, contacts, microphone, or camera.
Finally, the centralized nature of iOS updates news allows Apple to patch security vulnerabilities quickly and efficiently across hundreds of millions of devices simultaneously, a powerful tool against emerging threats.
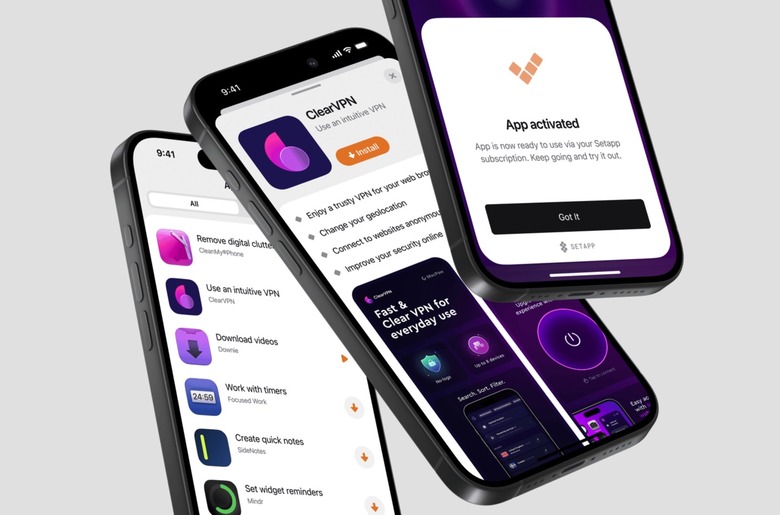
The New Frontier: Analyzing the Security of Alternative App Marketplaces
The introduction of alternative app marketplaces, while offering more choice, fundamentally changes the security equation. Apple’s implementation in regions like the EU is not a complete free-for-all; it includes a baseline security check called “Notarization.” However, it is crucial to understand how this differs from the full App Store review.
Notarization vs. Full App Review
Notarization is an automated process that scans apps for known malware and other critical security threats before they can be installed. It is a necessary but insufficient security layer when compared to the App Store’s process. Here’s the critical difference:
- Scope: Notarization primarily focuses on baseline security threats and platform integrity. It is not designed to check for the broad range of issues that human reviewers look for, such as deceptive business practices, privacy policy violations, or apps that offer a poor or misleading user experience.
- Human Oversight: The lack of mandatory human review means that novel threats, sophisticated scams, or apps that cleverly skirt the boundaries of privacy policies are more likely to slip through. An automated check can be gamed; a human reviewer is much harder to fool.
This creates a new landscape where the burden of trust shifts from Apple to the operator of the alternative marketplace and, ultimately, to the user.
Potential Vulnerabilities and Attack Vectors
The relaxation of Apple’s strict controls opens the door to several new attack vectors that users must be aware of. These threats could impact not just the iPhone but the entire connected ecosystem, from AirPods Pro news about firmware updates to the security of an Apple Watch.
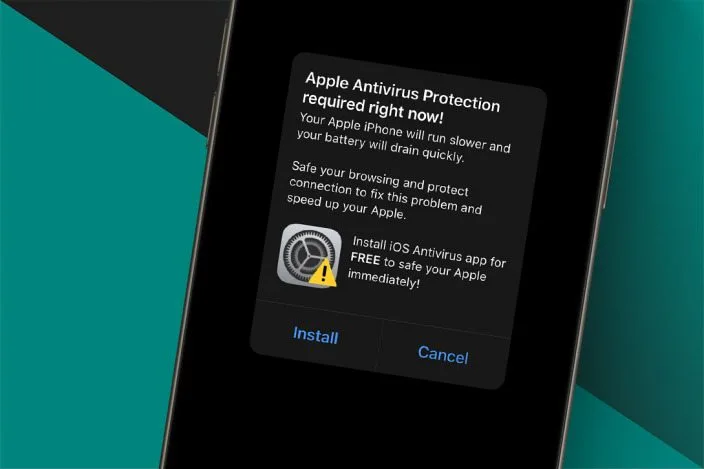
- Sophisticated Malware and Spyware: Without the full App Store review, there is a higher risk of apps containing spyware that monitors user activity, keyloggers that capture passwords, or ransomware that encrypts personal files. An app promising to bring back the glory days of the iPod, framed as exciting iPod revival news, could be a trojan horse for data theft.
- Privacy Erosion: Apps from alternative sources may not adhere to Apple’s App Tracking Transparency (ATT) framework or provide clear privacy labels. They could engage in aggressive data harvesting, selling user data to third parties without clear consent. This is particularly concerning for apps that handle sensitive information, a frequent topic in Apple health news.
- Financial Scams and Phishing: Alternative marketplaces could become a breeding ground for apps that mimic legitimate banking or shopping apps to steal financial information. They might also employ confusing subscription models or hidden fees that are explicitly forbidden on the App Store.
Real-World Implications: From User Privacy to Ecosystem Integrity
The theoretical risks of alternative marketplaces have tangible, real-world consequences for both individual users and the health of the broader Apple ecosystem. This shift is as significant as the latest Apple Vision Pro news, as it redefines a core part of the user experience.
The User’s Increased Burden of Responsibility
In Apple’s walled garden, the user is the beneficiary of a security model that works largely in the background. In the new model, the user becomes an active participant in their own security. This means they must now perform the due diligence that Apple previously handled. Before downloading an app from a new source, a user should ask:
- Is this marketplace reputable? What is its security policy?
- Who is the developer of this app? Do they have a professional presence and a history of creating safe software?
- Why is this app not on the official App Store?
Consider a scenario: A user downloads a “free” photo editing app touted on social media. The app, installed from a lesser-known marketplace, requests access to contacts, location, and photos. In the background, it exfiltrates this data to a remote server. The user may not notice anything is wrong until their contacts start receiving spam or their private photos appear online. This compromised device could then be used to attack other connected devices, from a HomePod mini to an Apple TV.
Impact on the Broader Apple Ecosystem
A key strength of Apple’s ecosystem is its seamless and secure integration. A security breach on one device can have cascading effects. Malware on an iPhone could potentially capture credentials for iCloud, giving an attacker access to photos, documents, and backups. It could attempt to exploit vulnerabilities to communicate with a paired Apple Watch or intercept commands sent via Siri news updates. The integrity of accessories, from an AirTag to an Apple Pencil, relies on the security of the host device. Even the development of apps for new platforms, as seen in iPad vision board news and Vision Pro accessories news, depends on a trusted software environment. A fragmented security landscape creates a “weakest link” problem, where a single unsafe app can undermine the security of a user’s entire digital life.
Navigating the New Landscape: Best Practices for iOS Users
While the new reality presents challenges, users are not powerless. Adopting a security-conscious mindset is the most effective way to mitigate the risks associated with alternative app marketplaces.
For the Cautious User: The Gold Standard
The simplest and most secure recommendation is to continue using Apple’s official App Store exclusively. It remains the safest place to acquire software for your iOS devices. For the vast majority of users, the selection and quality of apps on the App Store will meet all their needs without introducing unnecessary risk.
For the Adventurous User: A Security Checklist
If you choose to explore alternative marketplaces, it is critical to proceed with extreme caution. Treat it like venturing into an unknown territory and follow this checklist:
- Research the Marketplace: Do not use a marketplace without first researching its reputation, security policies, and app review process. Stick to larger, well-established alternatives if you must use one.
- Vet the Developer: Before installing an app, investigate the developer. Look for a professional website, a history of legitimate software, and user reviews from trusted sources. Be wary of unknown or anonymous developers.
- Scrutinize Permissions: When an app asks for permissions, think critically. Does a simple game really need access to your microphone and contacts? Deny any permissions that are not essential for the app’s core functionality.
- Avoid Sideloading from Untrusted Sources: Never install apps from a website link or a file sent to you via email or messaging. Only use official marketplaces.
- Keep iOS Updated: This is more important than ever. Install the latest iOS updates news as soon as they are available. These updates contain crucial security patches that protect the underlying operating system, which is your last line of defense.
Conclusion: A New Era of Choice and Responsibility
The arrival of alternative app marketplaces on iOS marks a pivotal moment for the platform. It introduces a new dynamic of user choice and developer freedom, but it undeniably comes with a significant trade-off in the baseline security and privacy guarantees that have long defined the iPhone experience. Apple’s walled garden, for all its criticisms of being restrictive, provides a powerful, centrally managed security framework that has protected millions from a myriad of threats. The new, more open model shifts a considerable portion of the security burden onto the user’s shoulders. Navigating this new era requires a heightened sense of awareness and vigilance. By understanding the risks, scrutinizing app sources, and adhering to security best practices, users can make informed decisions that allow them to explore the expanding Apple ecosystem news while safeguarding their digital lives.